How to Fix the FISA Court … Or Not
The government assures us that it does not maintain a database of incidentally collected information from non-targeted United States persons, and there is no evidence to the contrary. On these facts, incidentally collected communications of non-targeted United States persons do not violate the Fourth Amendment.(26)
That line, from the FISCR opinion finding the Protect America Act constitutional, gets to the core problem with the FISA Court scheme. Even in 2009, when the line was first made public, it was pretty clear the government had made a false claim to the FISA Court of Review.
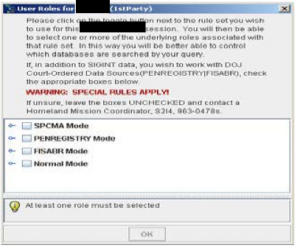
Now that we know that FBI had already been given authority to keep PAA-collected content in databases that they could search at what is now called the assessment stage of investigations — warrantless searches of the content of Americans against whom the FBI has no evidence of wrong-doing — the claim remains one of the signature moments where the government got approval for a program by being less than candid to the court (the government has been caught doing so in both Title III courts and at FISC, and continues to do so).
That’s also why I find Greg McNeal’s paper on Reforming the FISC, while very important, ultimately unconvincing.
McNeal’s paper is invaluable for the way he assesses the decision — in May 2006 — to authorize the collection of all phone records under Section 215. Not only does the paper largely agree with the Democratic appointees on PCLOB that the program is not authorized by the Section 215 statute, McNeal conducts his own assessment of the government’s application to use Section 215 for that purpose.
The application does not fare well.
Moreover, the government recognized that not all records would be relevant to an investigation, but justified relevance on what could best be described as usefulness or necessity to enable the government’s metadata analysis, stating:
The Application fully satisfies all requirements of title V of FISA. In particular, the Application seeks the production of tangible things “for” an international terrorism investigation. 50 U.S.C. § 1861(a)(1). In addition, the Application includes a statement of facts demonstrating that there are reasonable grounds to believe that the business records sought are “relevant” to an authorized investigation. Id. § 1861(b)(2). Although the call detail records of the [redacted] contain large volumes of metadata, the vast majority of which will not be terrorist-related, the scope of the business records request presents no infirmity under title V. All of the business records to be collected here are relevant to FBI investigations into [redacted] because the NSA can effectively conduct metadata analysis only if it has the data in bulk.49
The government went even further, arguing that if the FISC found that the records were not relevant, that the FISC should read relevance out of the statute by tailoring its analysis in a way that would balance the government’s request to collect metadata in bulk against the degree of intrusion into privacy interests. Disregarding the fact that the balancing of these interests was likely already engaged in by Congress when writing section 215, the government wrote:
In addition, even if the metadata from non-terrorist communications were deemed not relevant, nothing in title V of FISA demands that a request for the production of “any tangible things” under that provision collect only information that is strictly relevant to the international terrorism investigation at hand. Were the Court to require some tailoring to fit the information that will actually be terrorist-related, the business records request detailed in the Application would meet any proper test for reasonable tailoring. Any tailoring standard must be informed by a balancing of the government interest at stake against the degree of intrusion into any protected privacy interests. Here, the Government’s interest is the most compelling imaginable: the defense of the Nation in wartime from attacks that may take thousands of lives. On the other side of the balance, the intrusion is minimal. As the Supreme Court has held, there is no constitutionally protected interest in metadata, such as numbers dialed on a telephone.50
Thus, what the government asked the court to disregard the judgment of the Congress as to the limitations and privacy interests at stake in the collection of business records. Specifically, the government asked the FISC to disregard Congress’s imposition of a statutory requirement that business records be relevant, and in disregarding that statutory requirement rely on the fact that there was no constitutionally protected privacy interest in business records. The government’s argument flipped the statute on its head, as the purpose of enhancing protections under section 215 was to supplement the constitutional baseline protections for privacy that were deemed inadequate by Congress.
McNeal is no hippie. That he largely agrees and goes beyond PCLOB’s conclusion that this decision was not authorized by the statute is significant.
But as I said, I disagree with his remedy — and also with his assessment of the single source of this dysfunction.
McNeal’s remedy is laudable. He suggests all FISC decisions should be presumptively declassified and any significant FISC decision should get automatic appellate review, done by FISCR. That’s not dissimilar to a measure in Pat Leahy’s USA Freedom Act, which I’ve written about here. With my cautions about that scheme noted, I think McNeal’s remedy may have value.
The reason it won’t be enough stems from two things.
First, the government has proven it cannot be trusted with ex parte proceedings in the FISC. That may seem harsh, but the Yahoo challenge — which is the most complete view we’ve ever had of how the court works, even with a weak adversary — really damns the government’s conduct. In addition to the seemingly false claim to FISCR about whether the government held databases of incidentally collected data, over the course of the Yahoo challenge, the government,
- Entirely restructured the program — bringing the FBI into a central role of the process — without telling Reggie Walton about these major changes to the program the challenge he was presiding over evaluated; this would be the first of 4 known times in Walton’s 7-year tenure where he had to deal with the government withholding materially significant information from the court
- Provided outdated versions of documents, effectively hiding metadata that would have shown EO 12333, which was a key issue being litigated, was more fluid than presented to the court
- Apparently did not notice either FISC or FISCR about an OLC opinion — language from which was declassified right in the middle of the challenge — authorizing the President to pixie dust EO 12333 at any time without noting that publicly
- Apparently did not provide the underlying documents explaining another significant change they made during the course of the challenge, which would have revealed how easily Americans could be reverse targeted under a program prohibiting it; these procedures were critical to FISCR’s conclusion the program was legal
In short, the materials withheld or misrepresented over the course of the Yahoo challenge may have made the difference in FISCR’s judgment that the program was legal (even ignoring all the things withheld from Yahoo, especially regarding the revised role of FBI in the process). (Note, in his paper, McNeal rightly argues Congress and the public could have had a clear idea of what Section 702 does; I’d limit that by noting that almost no one besides me imagined they were doing back door searches before that was revealed by the Snowden leaks).
One problem with McNeal’s suggestion, then, is that the government simply can’t be trusted to engage in ex parte proceedings before the FISC or FISCR. Every major program we’ve seen authorized by the court has featured significant misrepresentations about what the program really entailed. Every one! Until we eliminate that problem, the value of these courts will be limited.
But then there is the other problem, my own assessment of the source of the problem with FISC. McNeal thinks it is that Congress wants to pawn its authority off onto the FISC.
The underlying disease is that Congress wants things to operate the way that they do; Congress wants the FISC and has incentives to maintain the status quo.
Why does Congress want the FISC? Because it allows them to push accountability off to someone else. If members ofCongress are responsible for conducting oversight of secretoperations, their reputations are on the line if the operations gotoo far toward violating civil liberties, or not far enoughtoward protecting national security. However, with the FISC conducting operations, Congress has the ability to dodge accountability by claiming they have empowered a court to conduct oversight.
I don’t, in general, disagree with this sentiment in the least. The last thing Congress wants to do is make a decision that might later be tied to an intelligence failure, a terrorist attack, a botched operation. Heck, I’d add that the last thing most members of Congress serving on the Intelligence Committees would want to do is piss off the contractors whose donations provide one of the perks of the seat.
But the dysfunction of the FISC stems, in significant part, from something else.
In his paper on the phone dragnet (which partly incorporates the Internet dragnet), David Kris suggests the original decision to bring the dragnets under the FISC (in the paper he was limited by DOJ review about what he could say of the Internet dragnet, so it is not entirely clear whether he means the Colleen Kollar-Kotelly opinion that paved the way for the flawed Malcolm Howard one McNeal critiques, or the Howard one) was erroneous. Read more →