9th Circuit Rules that Mohamed Osman Mohamud Might Have Killed Like a Bunch of White Mass Killers Had the FBI Not Intervened
The last paragraph of a 9th Circuit Judge John Owens opinion rejecting Mohamed Osman Mohamud’s appeal reads,
Many young people think and say alarming things that they later disavow, and we will never know if Mohamud—a young man with promise—would have carried out a mass attack absent the FBI’s involvement. But some “promising” young people—Charles Whitman, Timothy McVeigh, and James Holmes, to name a few from a tragically long list—take the next step, leading to horrific consequences. While technology makes it easier to capture the thoughts of these individuals, it also makes it easier for them to commit terrible crimes. Here, the evidence supported the jury’s verdict, and the government’s surveillance, investigation, and prosecution of Mohamud were consistent with constitutional and statutory requirements.
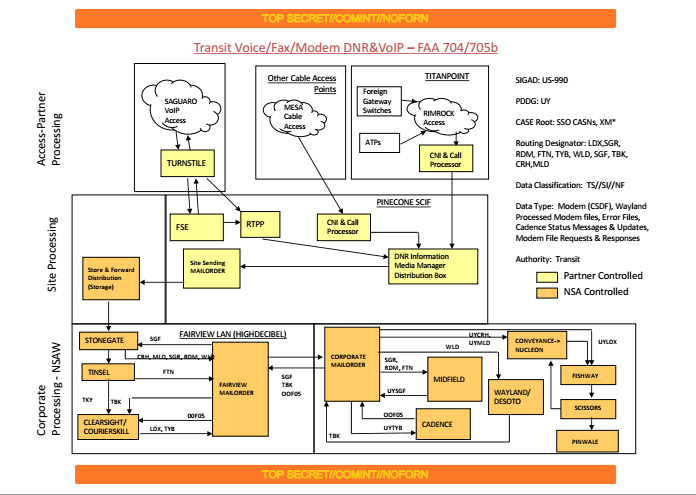
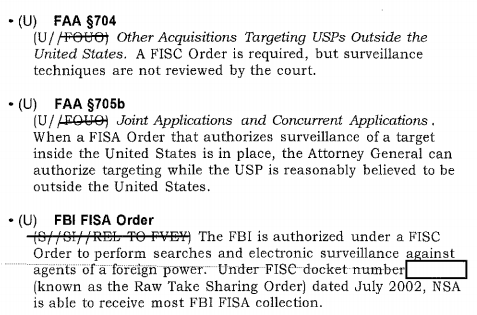
Mohamud had appealed on several grounds. Generally, he argued that he had been entrapped, that Section 702 was unconstitutional, and that that evidence should be thrown out because he was not informed in timely fashion.
The court was (as they had been in the hearing) most sympathetic to Mohamud’s entrapment case, but found that even though he was first approached before he turned 18 (Mohamud was 19 when he pressed a button believing it would set off a bomb at Portland’s Pioneer Square), the entrapment was less than what happened with James Cromitie, a case the 2nd Circuit upheld.
Nevertheless, the court found that a jury might reasonably find that Mohamud was predisposed to commit a bombing, even before government incitement.
In sum, viewing the evidence in the light most favorable to the government, we cannot say that “no reasonable jury could have concluded that [Mohamud was] predisposed to commit the charged offense[].” Davis, 36 F.3d at 1430. We therefore conclude that the district court properly rejected his defense of entrapment as a matter of law.
The court was less sympathetic to Mohamud’s FISA challenge.
But their argument on this front is pretty weird. The court dodges any ruling on a foreign intelligence exception that the government claimed.
Because the incidental collection excepts this search from the Fourth Amendment’s warrant requirement, we need not address any “foreign intelligence exception.”
Instead, it invokes the Third Party doctrine, suggesting that because Mohamud wrote to someone — anyone! — to suggest he had a diminished expectation of privacy in his side of emails.
It is true that prior case law contemplates a diminished expectation of privacy due to the risk that the recipient will reveal the communication, not that the government will be monitoring the communication unbeknownst to the third party. See, e.g., United States v. Miller, 425 U.S. 435, 443 (1976); United States v. White, 401 U.S. 745, 752 (1971); Hoffa v. United States, 385 U.S. 293, 302 (1966). While these cases do not address the question of government interception, the communications at issue here had been sent to a third party, which reduces Mohamud’s privacy interest at least somewhat, if perhaps not as much as if the foreign national had turned them over to the government voluntarily. See also Hasbajrami, 2016 WL 1029500 at *11 & n.18 (observing same distinction).
The court then admits that the sheer volume of incidental collection under Section 702 might be a problem, but suggests that minimization procedures thereby acquire more importance (while bracketing the problem of post-collection querying — also known as back door searches — the FBI conducts all the time).
Mohamud and Amici also contend that the “sheer amount of ‘incidental’ collection” separates § 702 from prior cases where courts have found such collection permissible. We agree with the district court’s observation that the most troubling aspect of this “incidental” collection is not whether such collection was anticipated, but rather its volume, which is vast, not de minimis. See PCLOB Report at 114 (“The term ‘incidental’ is appropriate because such collection is not accidental or inadvertent, but rather is an anticipated collateral result of monitoring an overseas target. But the term should not be understood to suggest that such collection is infrequent or that it is an inconsequential part of the Section 702 program.”). This quantity distinguishes § 702 collection from Title III and traditional FISA interceptions. However, the mere fact that more communications are being collected incidentally does not make it unconstitutional to apply the same approach to § 702 collection, though it does increase the importance of minimization procedures once the communications are collected.24
24 To the extent that Amici argue that the incidental overhear doctrine permits the unconstitutional and widespread retention and querying of the incidentally collected information, that issue is not before us.
Which brings us to this passage assessing the value of those minimization procedures with increased import.
While Executive Branch certification contributes some degree of further protection, it does not weigh heavily. Typically in the Fourth Amendment context, review from a neutral magistrate is considered the appropriate check on the Executive, which otherwise may be motivated by its interest in carrying out its duties. See, e.g., Leon, 468 U.S. at 913–14 (explaining that in obtaining a search warrant, a neutral magistrate is “a more reliable safeguard against improper searches than the hurried judgment of a law enforcement officer ‘engaged in the often competitive enterprise of ferreting out crime’” (citation omitted)). Under these circumstances, where the only judicial review comes in the form of the FISC reviewing the adequacy of procedures, this type of internal oversight does not provide a robust safeguard. The government notes that in In re Sealed Case, 310 F.3d 717, 739 (FISA Ct. Rev. 2002), the FISA Review Court observed that Congress recognized that certification by the AG in the traditional FISA context would “‘assure [ ] written accountability within the Executive Branch’ and provide ‘an internal check on Executive Branch arbitrariness.’” (citation omitted). However, as described above, § 702 differs in important ways from traditional FISA, and a mechanism that might provide additional protections above and beyond those already employed in a traditional FISA context provides far less assurance and accountability in the § 702 context, which lacks those baseline protections. See also Clapper, 133 S. Ct. at 1144–45.
Accordingly, although we do not place great weight on the oversight procedures, under the totality of the circumstnces, we conclude that the applied targeting and minimization procedures adequately protected Mohamud’s diminished privacy interest, in light of the government’s compelling interest in national security,
In other words, in the section assessing incidental collection, the court points to the import of minimization procedures. But when it comes to minimization procedures, it does “not place great weight” on them, because of the government’s compelling interest in national security. It is ultimately an argument about necessity based on national security.
Ultimately, then, the court argues that it was okay for the government to read Mohamud’s emails without a warrant, in spite of its admission of weaknesses in the government’s argument about a diminished expectation of privacy and minimization procedures. It does so by invoking three older (though still young) white mass killers, all of whom worked domestically.
While the court definitely relies on targeting rules limiting 702 to someone overseas, with its seeming admission that both its Third Party and its minimization procedure arguments are inadequate (as well as its decision that none of this has to do with a foreign intelligence exception), it gets frightfully close to making an argument that doesn’t distinguish foreign communications from domestic.
Perhaps Owens invokes those three white men to emphasize, unconvincingly, that that doesn’t mean Mohamud was targeted in a way a white non-Muslim wouldn’t be, but given the legal argument that’s left, the opinion is all the more troubling.
Update: Orin Kerr — who knows a lot more about law than I do — doesn’t like this opinion either. Among other common impressions, he’s not happy that Owens borrowed from a not really well written District opinion.