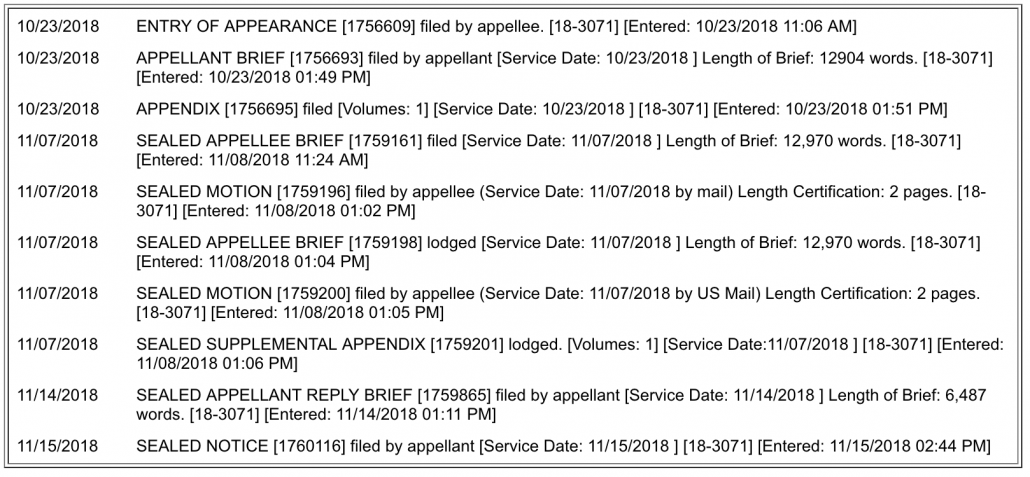
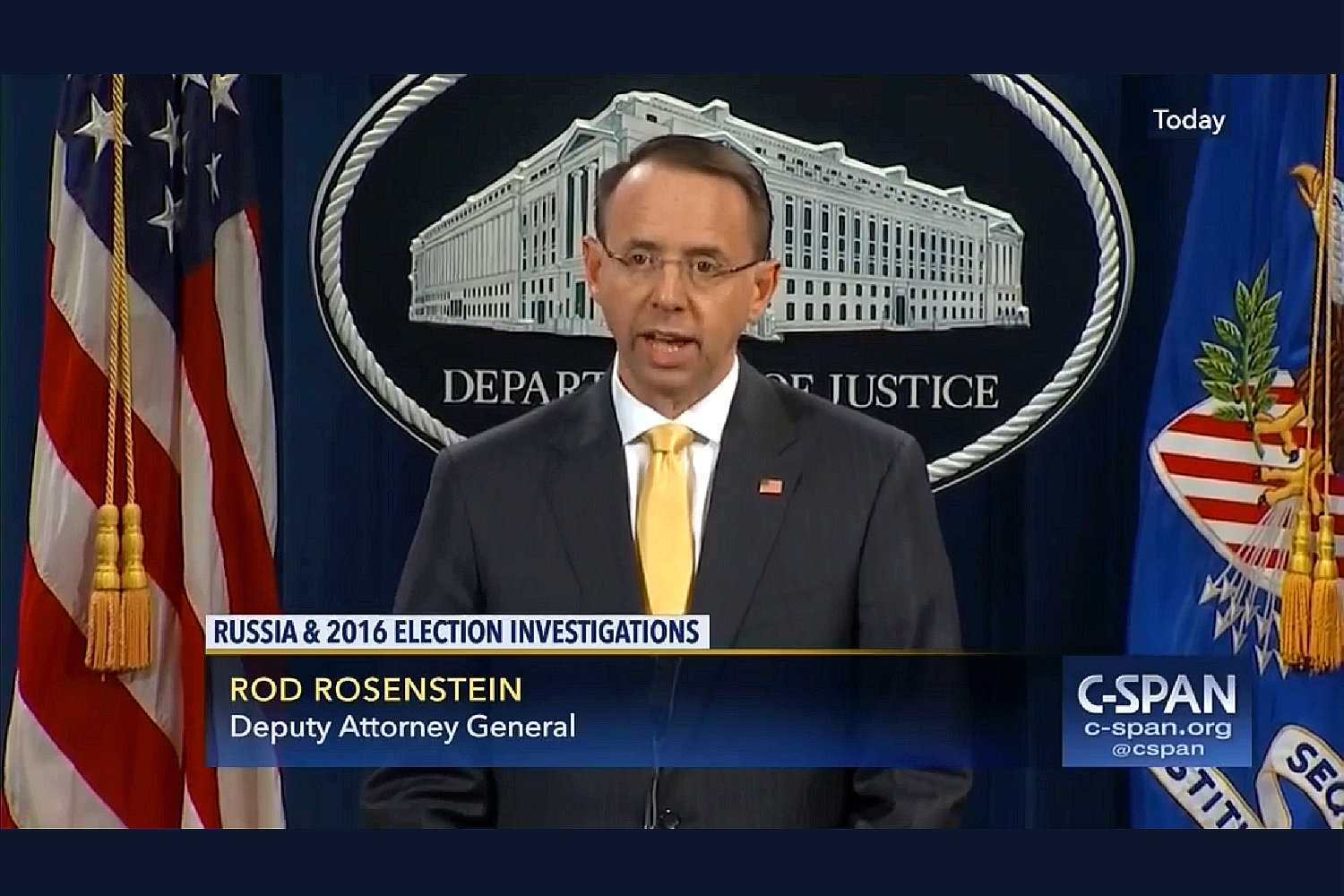
The WaPo confirmed something Seamus Hughes disclosed last night: Sometime before August 22, EDVA had filed a sealed complaint (not indictment) against Julian Assange.
WikiLeaks founder Julian Assange has been charged under seal, prosecutors inadvertently revealed in a recently unsealed court filing — a development that could significantly advance the probe into Russian interference in the 2016 election and have major implications for those who publish government secrets.
The disclosure came in a filing in a case unrelated to Assange. Assistant U.S. Attorney Kellen S. Dwyer, urging a judge to keep the matter sealed, wrote that “due to the sophistication of the defendant and the publicity surrounding the case, no other procedure is likely to keep confidential the fact that Assange has been charged.” Later, Dwyer wrote the charges would “need to remain sealed until Assange is arrested.”
Dwyer is also assigned to the WikiLeaks case. People familiar with the matter said what Dwyer was disclosing was true, but unintentional.
The confirmation closely follows a WSJ story describing increased confidence that the US will succeed in extraditing Assange for trial.
The confirmation that Assange has been charged has set off a frenzy, both among Assange supporters who claim this proves their years of claims he was indicted back in 2011 and insisting that charging him now would amount to criminalizing journalism, and among so-called liberals attacking Assange lawyer Barry Pollack’s scolding of DOJ for breaking their own rules.
I’ve long been on record saying that I think most older theories of charging Assange would be very dangerous for journalism. More recently, though, I’ve noted that Assange’s actions with respect to Vault 7, which had original venue in EDVA where the Assange complaint was filed (accused leaker Joshua Schulte waived venue in his prosecution), go well beyond journalism. That said, I worry DOJ may have embraced a revised theory on Assange’s exposure that would have dire implications for other journalists, most urgently for Jason Leopold.
There are, roughly, four theories DOJ might use to charge Assange:
- Receiving and publishing stolen information is illegal
- Conspiring to release stolen information for maximal damage is illegal
- Soliciting the theft of protected information is illegal
- Using stolen weapons to extort the US government is illegal
Receiving and publishing stolen information is illegal
The first, theory is the one that Obama’s DOJ rejected, based on the recognition that it would expose NYT journalists to prosecution as well. I suspect the Trump Administration will have the same reservations with such a prosecution.
Conspiring to release stolen information for maximal damage is illegal
The second imagines that Assange would be charged for behavior noted in the GRU indictment — WikiLeaks’ solicitation, from someone using the persona of Guccifer 2.0, of material such that it would be maximally damaging to Hillary Clinton.
On or about June 22, 2016, Organization 1 sent a private message to Guccifer 2.0 to “[s]end any new material [stolen from the DNC] here for us to review and it will have a much higher impact than what you are doing.” On or about July 6, 2016, Organization 1 added, “if you have anything hillary related we want it in the next tweo [sic] days prefable [sic] because the DNC [Democratic National Convention] is approaching and she will solidify bernie supporters behind her after.” The Conspirators responded, “ok . . . i see.” Organization 1 explained, “we think trump has only a 25% chance of winning against hillary . . . so conflict between bernie and hillary is interesting.”
After failed attempts to transfer the stolen documents starting in late June 2016, on or about July 14, 2016, the Conspirators, posing as Guccifer 2.0, sent Organization 1 an email with an attachment titled “wk dnc link1.txt.gpg.” The Conspirators explained to Organization 1 that the encrypted file contained instructions on how to access an online archive of stolen DNC documents. On or about July 18, 2016, Organization 1 confirmed it had “the 1Gb or so archive” and would make a release of the stolen documents “this week.”
Significantly, WikiLeaks (but not Roger Stone) was referred to in the way an unidicted co-conspirator normally is, not named, but described in such a way to make its identity clear.
This is a closer call. There is a Supreme Court precedent protecting journalists who publish stolen newsworthy information. But it’s one already being challenged in civil suits in ways that have elicited a lot of debate. Prosecuting a journalist for trying to do maximal damage actually would criminalize a great deal of political journalism, starting with but not limited to Fox. Note that when the founders wrote the First Amendment, the norm was political journalism, not the so-called objective journalism we have now, so they certainly didn’t expect press protections to be limited to those trying to be fair to both sides.
Such a charge may depend on the degree to which the government can prove foreknowledge of the larger agreement with the Russians to damage Hillary, as well as the illegal procurement of information after WikiLeaks expressed an interest in information damaging Hillary.
Mueller might have evidence to support this (though there’s also evidence that WikiLeaks refused to publish a number of things co-conspirators leaked to them, including but not limited to the DCCC documents). The point is, we don’t know what the fact pattern on such a prosecution would look like, and how it would distinguish the actions from protected politically engaged journalism.
Soliciting the theft of protected information is illegal
Then there’s the scenario that Emma Best just hit on yesterday: that DOJ would prosecute Assange for soliciting hacks of specific targets. Best points to Assange’s close coordination with hackers going back to at least 2011 (ironically, but in a legally meaningless way, with FBI’s mole Sabu).
This is, in my opinion, a possible way DOJ would charge Assange that would be very dangerous. I’m particularly worried because of the way the DOJ charged Natalie Mayflower Edwards for leaking Suspicious Activity Reports to Jason Leopold. Edwards was charged with two crimes: Unauthorized Disclosure of Suspicious Activity Reports and Conspiracy to Make Unauthorized Disclosures of Suspicious Activity Reports (using the same Conspiracy charge that Mueller has been focused on).
In addition to describing BuzzFeed stories relying on SARs that Edwards saved to a flash drive by October 18, 2017 and then January 8, 2018, it describes a (probably Signal) conversation from September 2018 where Leopold — described in the manner used to describe unindicted co-conspirators — directed Edwards to conduct certain searches for material that ended up in an October story on Prevezon, a story published the day before Edwards was charged.
As noted above, the October 2018 Article regarded, among other things, Prevezon and the Investment Company. As recently as September 2018, EDWARDS and Reporter-1 engaged in the following conversation, via the Encrypted Application, in relevant part:
EDWARDS: I am not getting any hits on [the CEO of the Investment Company] do you have any idea what the association is if I had more information i could search in different areas
Reporter-1: If not on his name it would be [the Investment Company]. That’s the only other one [The CEO] is associated with Prevezon Well not associated His company is [the Investment Company]
Based upon my training and experience, my participation in the investigation, and my conversations with other law enforcement agents familiar with the investigation, I believe that in the above conversation, EDWARDS was explaining that she had performed searches of FinCEN records relating to Prevezon, at Reporter-l’s request, in order to supply SAR information for the October 2018 Article.
Edwards still has not been indicted, two weeks after her arraignment. That suggests it’s possible the government is trying to persuade her to plead and testify against Leopold in that conspiracy, thereby waiving indictment. The argument, in that case, would be that Leopold went beyond accepting stolen protected information, to soliciting the theft of the information.
This is the model a lot of people are embracing for an Assange prosecution, and it’s something that a lot of journalists not named Jason Leopold also do (arguably, it’s similar but probably more active than what James Rosen got dubbed a co-conspirator in the Stephen Jin-Woo Kim case).
Charging Leopold in a bunch of leaks pertaining to Russian targets would be a nice way (for DOJ, not for journalism) to limit any claim that just Assange was being targeted under such a theory. Indeed, it would placate Trump and would endanger efforts to report on what Mueller and Congress have been doing. Furthermore, it would be consistent with the aggressive approach to journalists reflected in the prosecution of James Wolfe for a bunch of leaks pertaining to Carter Page, which involved subpoenaing years of Ali Watkins’ call records.
In short, pursuing Leopold for a conspiracy to leak charge would be consistent with — and for DOJ, tactically advantageous — the theory under which most people want Assange charged.
Using stolen weapons to extort the US government is illegal
Finally, there’s the fourth possibility, and one I think is highly likely: charging Assange for his serial efforts to extort a pardon from the US government by threatening to release the Vault 7 (and ultimately, a single Vault 8 live malware) files.
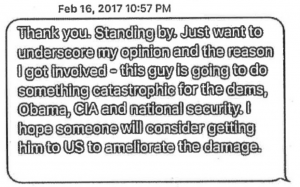
This post shows how, starting in January 2017, Assange (and Oleg Deripaska) representative Adam Waldman was reaching out to top DOJ officials trying to negotiate a deal and using the release of the Vault 7 documents as leverage.
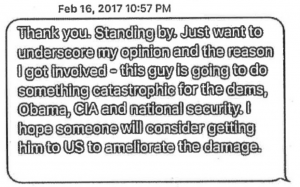
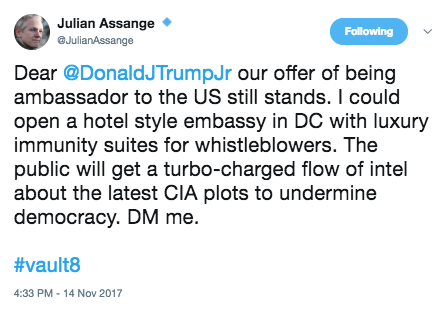
This post shows how, the second time Assange tweeted Don Jr asking for an Ambassadorship, he included a threatening reference to Vault 8, WikiLeaks’ name for the actual malware stolen and leaked from CIA, the first file from which Assange had released days earlier.
[B]ack in November 2017, some outlets began to publish a bunch of previously undisclosed DMs between Don Jr and Wikileaks. Most attention focused on Wikileaks providing Don Jr access to an anti-Trump site during the election. But I was most interested in Julian Assange’s December 16, 2016 “offer” to be Australian Ambassador to the US — basically a request for payback for his help getting Trump elected.
Hi Don. Hope you’re doing well! In relation to Mr. Assange: Obama/Clinton placed pressure on Sweden, UK and Australia (his home country) to illicitly go after Mr. Assange. It would be real easy and helpful for your dad to suggest that Australia appoint Assange ambassador to DC “That’s a really smart tough guy and the most famous australian you have! ” or something similar. They won’t do it, but it will send the right signals to Australia, UK + Sweden to start following the law and stop bending it to ingratiate themselves with the Clintons. 12/16/16 12:38PM
In the wake of the releases, on November 14, 2017, Assange tweeted out a follow-up.
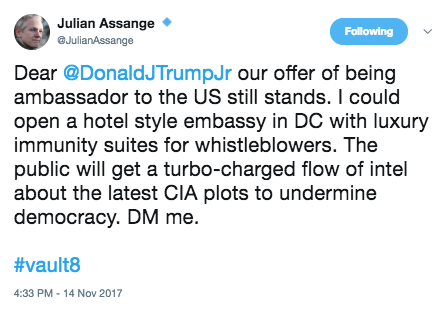
As I noted at the time, the offer included an implicit threat: by referencing “Vault 8,” the name Wikileaks had given to its sole release, on November 9, 2017 of an actual CIA exploit (as opposed to the documentation that Wikileaks had previously released), Assange was threatening to dump more hacking tools, as Shadow Brokers had done before it. Not long after, Ecuador gave Assange its first warning to stop meddling in other countries politics, explicitly pointing to his involvement in the Catalan referendum but also pointing to his tampering with other countries. That warning became an initial ban on visitors and Internet access in March of this year followed by a more formal one on May 10, 2018 that remains in place.
Notably, Ecuador may have warned Assange back then to stop releasing America’s malware from their Embassy; those warnings have laid the groundwork for the rigid gag rules recently imposed on Assange on risk of losing asylum.
Immediately after this exchange, accused Vault 7/8 leaker Joshua Schulte had some Tor accesses which led to him losing bail. They didn’t, however, lead BOP to take away his multiple devices (!?!?!). Which means that when they raided his jail cell on or around October 1, they found a bunch of devices and his activity from 13 email and social media accounts. Importantly, DOJ claims they also obtained video evidence of Schulte continuing his efforts to leak classified information.
The announcement of that raid, and the additional charges against Schulte, coincided with a period of increased silence from WikiLeaks, broken only by last night’s response to the confirmation Assange had been charged.
I think it possible and journalistically safe to go after Assange for releasing stolen weapons to extort a criminal pardon. But most of the other theories of prosecuting Assange would also pose real risks for other journalists that those rooting for an Assange prosecution appreciate and rely on.
As I disclosed in July, I provided information to the FBI on issues related to the Mueller investigation, so I’m going to include disclosure statements on Mueller investigation posts from here on out. I will include the disclosure whether or not the stuff I shared with the FBI pertains to the subject of the post.